Explore the Roam World
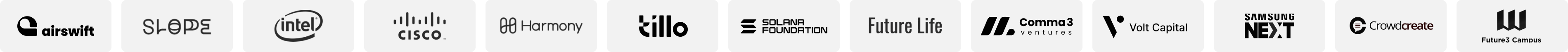
Add WiFi To Earn
Expand Roam network and earn rewards for every WiFi spot added.
Check-In Rewards
Earn mPoints simply by checking in daily to boost your rewards portfolio.
Explore the Roam World
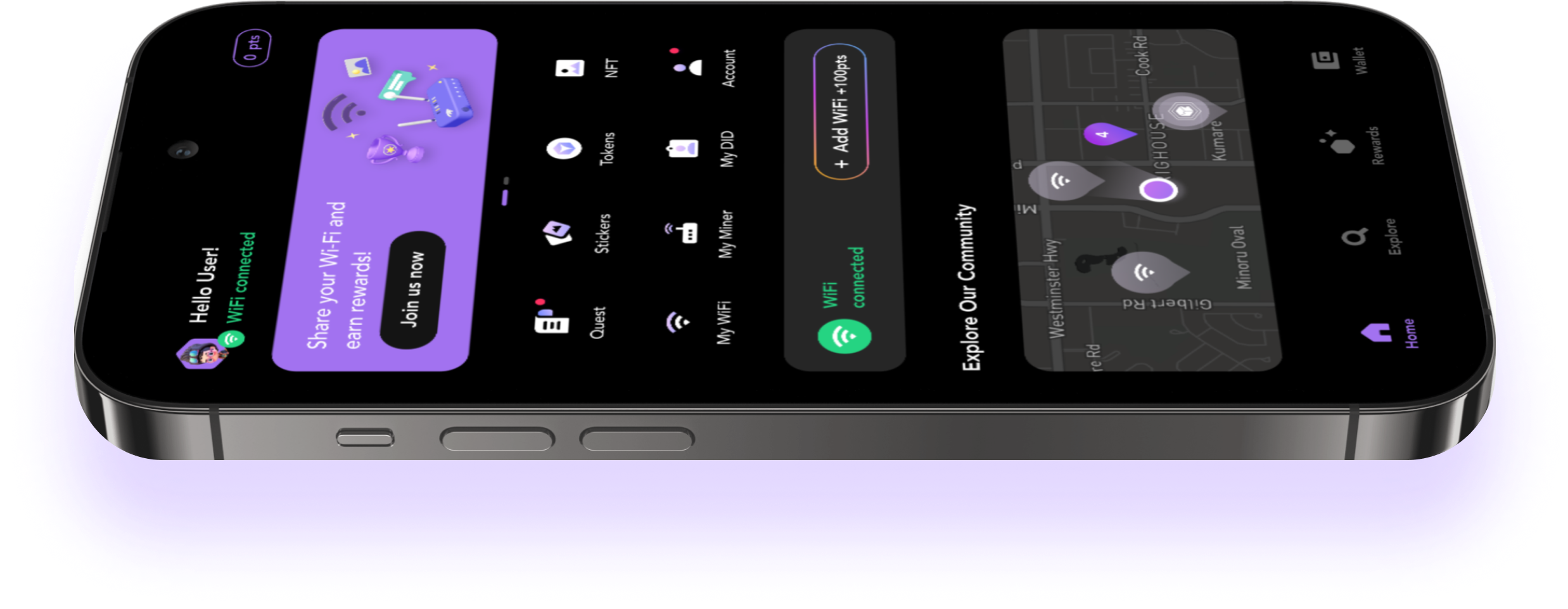
Add WiFi To Earn
Expand Roam network and earn rewards for every WiFi spot added.
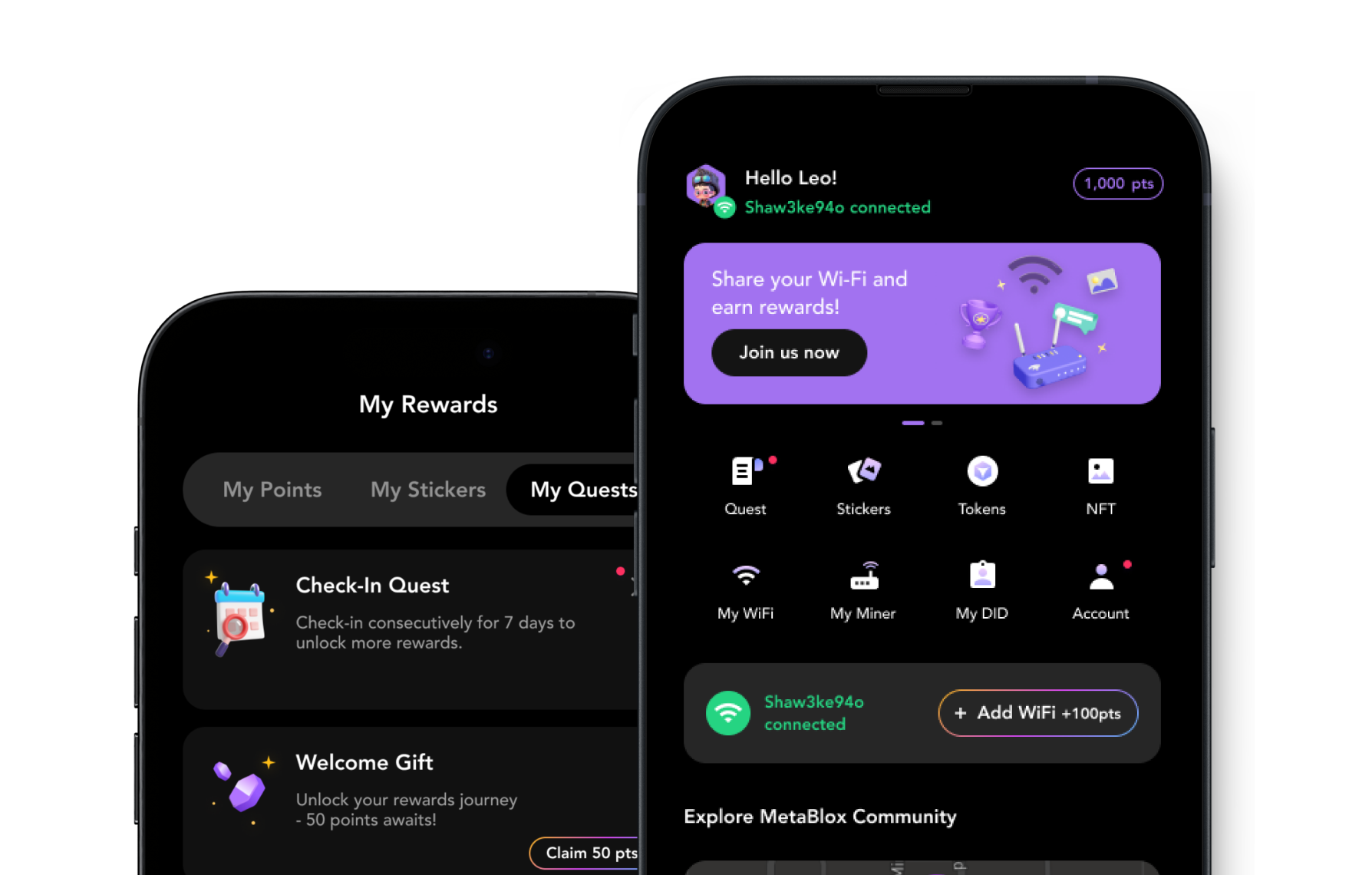
Check-In Rewards
Earn mPoints simply by checking in daily to boost your rewards portfolio.
Underlying Technology
The power of Roam Network
Standing at the forefront of the DeWi Space, Roam is changing the way people connect and setting a new standard for reliable and efficient WiFi. Download Roam now to start a journey filled with millions of free WiFi access points and exclusive rewards.
The power of Roam Network
Standing at the forefront of the DeWi Space, Roam is changing the way people connect and setting a new standard for reliable and efficient WiFi. Download Roam now to start a journey filled with millions of free WiFi access points and exclusive rewards.
Loading
Our Partners
Our esteemed partners play a pivotal role in shaping the future alongside us. Together, we embark on a journey of innovation and progress. Learn more about our partners and their impact.
The Roam Community
Roam's goal is to nurture a vibrant and active community. By joining our community on various channels, you'll have access to exclusive content, participate in exciting discussions, and stay up-to-date with our latest news and events.